Randomness underpins security by transforming predictable processes into unpredictable ones, constraining an adversary’s foresight. It strengthens keys, nonces, and state transitions, making attacks computationally or statistically unlikely. Entropy sources vary—from quantum phenomena to hardware generators and pseudorandom constructs—each with distinct assumptions. Systematic bias checks and continuous auditing reveal residual skew and guide calibration. The discipline of entropy management sustains protocol integrity under operational conditions, though practical guarantees depend on chosen sources and verification rigor.
What Makes Randomness Essential for Security
Randomness underpins security by converting predictable processes into unpredictable ones, thereby limiting an adversary’s ability to anticipate outcomes. In this context, randomness supplies measured uncertainty that strengthens system resilience.
Security guarantees rely on robust entropy measurement to quantify this uncertainty, ensuring reproducibility across implementations.
The disciplined application of entropy assessment supports consistent, transparent risk management and trustworthy cryptographic foundations for freedom-loving stakeholders.
How Unpredictable Randomness Protects Keys and Protocols
Unpredictable randomness fortifies cryptographic keys and protocols by limiting adversaries’ ability to forecast credentials, nonces, and state transitions. The discussion analyzes resilience, showing how entropy compounds resistance against prediction.
Attention to entropy pitfalls clarifies potential weaknesses, while seed stability ensures reproducible security properties under operational conditions.
Rigorous assessment emphasizes disciplined randomness management, minimizing exposure and preserving protocol integrity for users seeking freedom.
Sources of Randomness: From Quantum to Pseudorandom Generators
This section surveys the principal sources of randomness used in cryptography, tracing a path from quantum phenomena to deterministic, reproducible generators.
Quantum entropy arises from fundamental indeterminacy, providing unpredictable seeds.
Pseudorandom generators convert structured inputs into long streams that mimic randomness under rigorous statistical tests.
The spectrum spans hardware-derived entropy sources and algorithmic constructions, each with distinct guarantees, limitations, and security assumptions.
Verifying Fairness and Absence of Bias in Randomness
Building confidence in cryptographic randomness requires systematic assessment of fairness and the absence of bias. The analysis employs bias checks to detect disproportionate outcomes and metrology to guard against preferential patterns. Entropy auditing quantifies unpredictability, validating uniform distribution assumptions. Thorough evaluations disclose residual biases, inform corrective calibrations, and sustain trust in random sources essential for secure protocols and freedom from covert influence.
Frequently Asked Questions
How Does Randomness Impact Real-World Attack Scenarios?
The randomness impact manifests as unpredictability complicating adversaries, reducing success in real world attacks; extreme hardware and failure conditions may degrade entropy sources, amplifying risk, yet rigorous designs mitigate exposure through redundancy, validation, and continuous monitoring under adversarial conditions.
Can Randomness Fail Under Extreme Hardware Conditions?
Answering: Yes, randomness can fail under extreme hardware, with one statistic noting correlated failures in 0.01–0.1% of devices under stress. Thus randomness failure may occur when extreme hardware conditions arise, challenging security guarantees.
Do Humans-In-The-Loop Processes Introduce Biases in Randomness?
Humans-in-the-loop processes can introduce bias exposure, as cognitive heuristics influence choices, yet careful design mitigates such effects. Robust entropy sourcing and auditability limit bias exposure, preserving unpredictability while enabling transparency for an audience seeking freedom.
What Are Trade-Offs Between Speed and Randomness Quality?
The trade-offs between speed vs randomness quality depend on system requirements; faster generation often relies on faster, less unpredictable sources. Hardware entropy sources enhance quality but may constrain throughput, demanding careful balancing of hardware capabilities and security expectations.
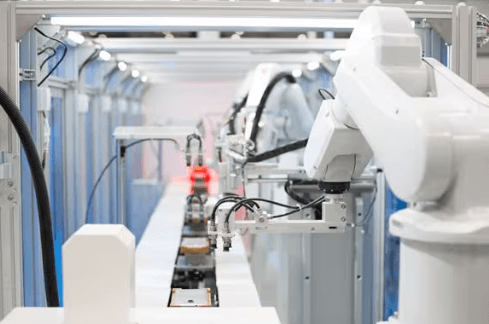
See also: Smart Sensors in Manufacturing
How Is Randomness Auditor-Independent Verification Performed?
Auditing entropy is conducted via auditing entropy sources and reproducible sources, with independent evaluation and documentation. The process uses formal procedures, preserving transparency while respecting freedom, ensuring auditor-independent verification through verifiable randomness derivation, reproducible source data, and controlled validation workflows.
Conclusion
In this landscape, randomness stands as a silent sentinel, cloaked in the mantle of uncertainty. It sketches a map where keys whisper identities only to the legitimate holder, and protocols tread securely through uncharted futures. Symbolically, entropy becomes the impartial clock, ticking away predictability while preserving order. With rigorous auditing and diverse sources, the random becomes trustworthy: a keystone that, unseen, supports resilience, fairness, and the seamless, auditable reliability of modern security.